Veracode’s 2026 State of Software Security Report Reveals Alarming Trends in Application Risk
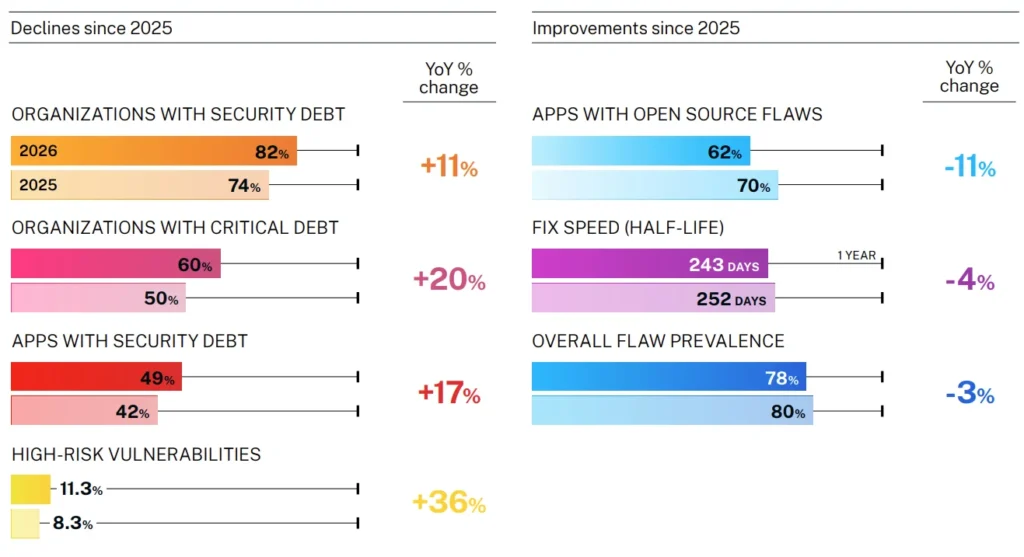
Why is the gap between software development speed and security remediation widening? Veracode, a global leader in application risk management, has released its 2026 State of Software Security Report, which highlights a critical issue: the rapid increase in high-risk vulnerabilities and critical security debt. The report, based on an analysis of 1.6 million unique applications, reveals a 36% year-over-year spike in high-risk vulnerabilities and a 20% increase in critical security debt, signaling a growing crisis in software security.
The report underscores a fundamental mismatch between the velocity of software development and the capacity to secure it. Despite improvements in detection capabilities, the backlog of unresolved vulnerabilities is growing faster than teams can address them. “The speed of software development has skyrocketed, meaning the pace of flaw creation is outstripping the current capacity for remediation,” said Chris Wysopal, Chief Security Evangelist at Veracode. This trend is exacerbated by the introduction of AI, which is both accelerating development and introducing new high-risk vulnerability patterns.
Key Insights at a Glance
- Security Debt: 82% of organizations now harbor security debt, a 11% increase from the prior year.
- Critical Debt: 60% of organizations have critical security debt, representing vulnerabilities that could cause catastrophic damage.
- High-Risk Flaws: High-risk vulnerabilities have increased by 36% year-over-year.
- Open-Source Risks: Third-party libraries and open-source dependencies account for 66% of the most dangerous, longest-lived vulnerabilities.
- AI Impact: AI is introducing new high-risk vulnerability patterns while offering potential solutions for remediation.
Why Security Debt Is a Growing Crisis
The accumulation of security debt is outpacing remediation efforts, creating a significant risk for organizations. The report found that 82% of organizations now have security debt, with 60% of these organizations facing critical levels of debt. This means that vulnerabilities are accumulating faster than they can be fixed, leaving organizations vulnerable to potential attacks. The urgency is clear: organizations must rethink how they manage their security backlogs to prevent catastrophic breaches.
The Regulatory Clock Is Ticking for Software Security
Just as a ticking time bomb, the growing security debt poses an imminent threat to organizations. Veracode’s report highlights the need for a strategic approach to managing vulnerabilities. The 36% year-over-year increase in high-risk vulnerabilities, combined with the 20% rise in critical security debt, underscores the critical window of opportunity for action. Like a skilled surgeon, organizations must prioritize the most dangerous flaws and implement automated remediation to protect their critical assets.
Veracode’s Strategic Framework: Protect, Prioritize, and Prove
Veracode is advocating for a shift from simple detection to a more strategic framework of Prioritize, Protect, and Prove. This approach involves identifying the most critical vulnerabilities, protecting the most valuable systems, and proving that the security posture meets modern compliance standards. “We are at an inflection point where running faster on the treadmill of vulnerability management is no longer a viable strategy,” Wysopal emphasized. “Success requires a deliberate shift. Teams must prioritize the 11.3% of flaws that pose real-world danger, protect their critical assets through automated remediation, and prove that their security posture meets the rigorous demands of modern compliance.”
Future Outlook
The landscape of software security is evolving rapidly, driven by AI and the increasing complexity of software development. Veracode’s report suggests that while AI is introducing new challenges, it also offers promising solutions for automated remediation. The company’s annual State of Software Security Report continues to provide one of the most comprehensive views of the application risk management landscape. Join the webinar on February 26 at 11am Eastern Time to hear from the authors of this year’s report and gain deeper insights into the key findings.
Conclusion
The 2026 State of Software Security Report by Veracode highlights a critical issue that every organization must address: the growing gap between software development speed and security remediation. How is your firm preparing for this shift? Join the conversation in the comments below.
About the State of Software Security Report
The Veracode State of Software Security draws on analysis of applications tested through static analysis, dynamic analysis, software composition analysis, and/or manual penetration testing through Veracode’s cloud-based platform. This year’s dataset includes 1.6 million unique applications generating 141.3 million raw findings—115.6 million from static analysis, 22.1 million from software composition analysis, and 3.6 million from dynamic analysis. This data spans companies of all sizes, commercial software suppliers, software outsourcers, and open-source projects worldwide.
About Veracode
Veracode is a global leader in Application Risk Management for the AI era. Powered by trillions of lines of code scans and a proprietary AI-assisted remediation engine, the Veracode platform is trusted by organizations worldwide to build and maintain secure software from code creation to cloud deployment. Thousands of the world’s leading development and security teams use Veracode every second of every day to get accurate, actionable visibility of exploitable risk, achieve real-time vulnerability remediation, and reduce their security debt at scale. Veracode is a multi-award-winning company offering capabilities to secure the entire software development life cycle, including Veracode Fix, Static Analysis, Dynamic Analysis, Software Composition Analysis, Container Security, Application Security Posture Management, Malicious Package Detection, Package Firewall, and Penetration Testing.
Source link: https://www.businesswire.com/